|
It was Johnny Rotton who shouted so wildly
'the futures dream is a shopping spree'
and it seems to be the case
Earlier this week [july 2004] Home secretary [now gone hooray!] David Blunkett introduced Blair to the police conference...
he used the phrase 'prison without borders'.
and went on to introduce new plans to tag 5000 criminals
under a GPS securitys watchful eye.
The news media belts out the false premise that a
criminal watched is a criminal stopped...
think about it... there are more cameras per square yard in this country
than in any other...yet the powers that be tell us that crime is still rising.
|
Rise and rise of violent crime mars overall fall in offences
The latest figures show an alarming increase in the use of imitation guns
VIOLENT crime rose 9 per cent in the last three months of 2004 with firearms offences involving imitation weapons soaring by 66 per cent, according to figures published yesterday.
The number of violent offences recorded by police in England and Wales reached almost 300,000, with the most serious crimes increasing by 11 per cent. The overall number of crimes recorded by the police fell by 5 per cent in the last quarter of the year compared with the same period in 2003.
Figures from the separate British Crime Survey, which interviews 40,000 people on their experience of crime, show an 11 per cent fall in overall crime.
An estimated 3,210 violent offences a day are recorded in England and Wales and, if estimates of underreporting are taken into account, the figure could be as high as 12,840. The rise in recorded violent crime, along with an increase in the percentage of people who think people being drunk and rowdy on the streets is a problem, forced ministers on to the defensive during the election campaign.
Charles Clarke, the Home Secretary, promised new legislation to tackle the use of imitation firearms and knives on the streets if Labour is re-elected. He told a press conference shortly before the crime figures were published that a violent crime reduction Bill would be introduced within weeks if Labour won the election.
It would tackle the ownership and use of replica firearms and knives, propose tougher sentences for knife and gun crime and new measures on antisocial behaviour.
The Prime Minister said that crime had fallen under Labour but added: "We know that for many people in local communities it doesn't feel like that."
Times online
|
wouldn't this suggest to any fool, that the cameras just ain't working!
that indeed people just get used to them and go for it big style...anyway
I, for one, have never understood how a camera stops anyone doing anything...
...and there-in lies the reason why this is all being done...
The element of fear driven by crime is being used within this technology in order to
bribe the population to take part in a social experiment...
...and still the proposals are made, only in this ultra-modern present
instead of visible cameras looking over us taking a quiet piss in an alleyway,
the cameras are to be hidden in the sky...we are to be chipped,
[for our own safety, of course].
to see what the near future holds for us is to turn to the DNA database.
Something which i fear is the extension of the demographic tabulating Hollerith machine,
which was used to very sinister ends by the Nazis in WWII...counting, labelling people miscreants
thus enabling them to experiment on them & kill them...
[this should be a lesson to us all- ALWAYS LIE ON QUESTIONAIRES- polls etc]
We are constantly reassured that this biotechnology is to be used as a means to find
the cure for cancer, AIDS, Alzheimers etc...
but where is this cure ? it must be 20-30 years and the promises are STILL coming!
|
Promises, Promises, sounds like a 10 year plan...
|
what have they been up to?
They have been designing diseases that can be patented and propogated
in order to keep us in line...
the same behavioristic model that is used with Cameras and tracking is to be
introduced very soon via Micro-electronic machines [MEMS], into cells & viral bacteria
There are reports of Magnetic resonance imaging being experimented with and
used within Huge advertising hoardings...
indeed this technology- a walk through scanner
is being utilised to check for weapons outside
clubs in London
This is Orwells two way mirror to your soul...
Future use of F-MRI [a magnetic resonance imager that reads brain activity in real time] will be an open x-ray to you brains activity...
such as the current dreams of neuro marketing...which is cutely referred to
as 'pressing the buy button of the brain...
if this technology can be used to press a 'buy button'...
what other buttons can be pressed?
the fear button?
the docility button?
the death button?
vast waves of this energy will flow from advertising screens in malls, and along
highways could well be be used as a immune system debilitator, which will allow the
influence of mood controlling via induced feelings of sickness/well-being...
feelings in which even an incremental amount give rise to a feeling of being
under the weather, or 'not myself today'...
and in the tradition of Delgado & Skinner, if one makes people feel slighly ill
during certain activity, ooh say, like crossing a geo-fencing boundary,
they will be far less likely to continue...
see:
Operant Conditioning and Behaviorism - an historical outline
this headline really does say it all:
Terror fears boost new security gadgets
By Kevin Anderson - BBC News Online in Las Vegas
In the late 1990s, AC Technology had a system to match composite sketches to mugshots. The problem was that "there was really no cash in that cash drawer," said Gregg Gerlach, the company's CTO. Law enforcement agencies simply didn't have the money to buy the system.
But, he said, that all that changed following the 11 September attacks.
The company has adapted its face recognition technology and is one of many companies at the Comdex trade show in Las Vegas marketing their systems for the use in the US government's homeland security initiatives.
Governments open coffers
Business spending - especially on technology - is down.
Companies have slashed costs and are delaying upgrading computers and software until absolutely necessary.
But defence and security spending is up, and both the US and UK governments are exploring face recognition and other biometric technologies to enhance security.
Biometrics uses physical traits such as fingerprints, facial features, or patterns in the iris or retina of the eye to positively identify a person.
Biometrics stocks have risen 130% since 11 September 2001
The UK Home Office is working on a programme to speed entry at airports by visitors from other countries by using biometrics. And the US has mandated that by 2004 foreign visitors will have to carry travel documents with biometric identifiers such as fingerprints.
Biometric scans are being used to provide greater security at airports, nuclear power plants or sensitive government or military facilities.
Access to the offices of US Vice President Dick Cheney is restricted using iris-recognition technology.
It is a nascent industry, worth between $240m to $400m, according to Brian Ruttenbur, senior vice president and equity research analyst with Morgan Keegan & Company. But stocks in biometric companies have risen 130% after the 11 September attacks, he said.
Focus on security
AC Technology is just one of a growing number of companies in the biometric industry. Mr Ruttenbur estimates that there between 250 and 400 companies involved in biometrics. The technology has a strong presence at the Comdex trade fair, taking place this week in Las Vegas. Biometrics companies have their own special section on the floor of the show. And the UK@Comdex booth is highlighting pattern recognition technology developed at the University of York used in face recognition systems as well as the pioneering work of John Daugman, who invented the mathematical algorithms used in all iris-recognition systems.
Companies are building it into all kinds of devices.
The industry is experiencing an initial flowering
HP introduced a high-end handheld computer with fingerprint-based security built in, and one company is selling a tiny flash memory device with a fingerprint-based lock. SAFLINK has a large booth at Comdex demonstrating a wide range of biometric security devices. On one computer, a user must scan their fingerprint to log on. Users don't have to remember a password. But if they step away from their terminal, a proximity sensor is triggered and automatically logs users off, forcing them to rescan their fingerprint to log on again.
No profits, just pilots
However, while governments are rushing to implement the systems, most of the programmes are still in the pilot phase. EyeTicket's iris-recognition system was tested recently at Heathrow to speed frequent travellers from North America through immigration.
But the company's CEO, Stewart Mann said, "I don't know a single [biometrics] company that is making money yet."
However, companies expect the money to start flowing soon. The recent elections in the US in which Republicans gained control of both houses of Congress will help speed the process, said Glenn Argenbright, president and CEO of SAFLINK. And on Tuesday the newly reconstituted Senate approved President Bush's plan to create a Department of Homeland Security by a vote of 90-9.
But Mr Ruttenbur expects a dramatic consolidation in the industry. Companies that have early wins on key contracts will survive, but Mr Ruttenbur predicts that of the several hundred biometric companies, only about 50 will remain in five years. - BBC
|
Terror! It's GOOD for the ECONOMY!!!

What's Hot Today: Homeland Security
Technologies Vie For A Share Of The Expanding Homeland Security Budget
Ultimately, this market will resemble the early biotechnology market, where startups developed new technologies and partnered with the established pharmaceutical houses to deal with Food and Drug Administration requirements, as well as with marketing and sales.
In fact, this is already happening. A small Canadian company, Exploranium, had a technology for radiological detection in scrap metal. Science Applications International Corp. (SAIC) recently acquired Exploranium, and now the technology is being incorporated into its mobile Vehicle and Cargo Inspection System (VACIS). A truck-mounted, non-intrusive gamma-ray imaging system, VACIS produces radiographic images used to evaluate the contents of trucks, containers, cargo, and passenger vehicles. The Exploranium technology adds radiological detection to the mix.
More than a dozen companiesincluding Boeing, Lockheed Martin, and Raytheonare as big or bigger than SAIC, and they have the infrastructure and experience for dealing with government programs. In addition, many smaller companies currently research and develop technologies and products related to homeland security.
For example, SafeView Inc. was established in 2002 to commercialize a patented holographic process (developed by Pacific Northwest National Laboratory). Using a non-ionizing process based on active millimeter-wave technology, SafeView's process enables users to clearly see objects made of metal, plastic, ceramic, and other materials hidden among clothing in luggage.
Another example of symbiosis is Analogic's work with Sanders Design International to forge an effective countermeasure system for commercial airliners that would help protect them from attack by shoulder-fired, heat-seeking missiles. Analogic also is working with Lockheed Martin on detection devices for passenger carryon luggage scrutiny. source
|
Airports - behavioral conditioning - don't look suspicious...
|
Logan troopers to get roving database access
Critics see threat to privacy rights in antiterrorism move
By Keith Reed, Globe Staff | June 22, 2004 - Boston.com
State troopers at Logan International Airport will have instant access to a wealth of personal information on nearly every person who passes through the airport, from Social Security numbers to names of former roommates.
All that information will be at the fingertips of troopers at Logan, under a deal between the Massachusetts State Police and LocatePlus Holdings Corp., a Beverly company that collects public records about individuals and rents access to the information to law enforcement agencies.
Officers in Troop F, the State Police unit at Logan, are getting wireless BlackBerry devices linked to LocatePlus's database that includes 7 billion records containing information on 98 percent of the adults in the United States. That could include anything from unlisted phone numbers to names on a lease.
When a trooper stops a person acting suspiciously at the airport, he could enter that person's name into the device, which would search for information about his or her identity, past associations, and activities.
State Police and LocatePlus officials said yesterday that giving police access to personal information on people they stop at the airport could prove critical in identifying potential terrorist suspects or thwarting other crimes. For example, since the database lists previous addresses and names on a lease, such information can help an officer determine whether someone lived or otherwise associated with alleged terrorists.
"A name, that's all he needs," said LocatePlus chief executive Jon Latorella. "He can find out who you lived with, where you lived, anything about you. We have every unlisted phone number in the country. Our stuff is instant, instead of having to wait until after the fact of a bombing."
It's that instant access to personal information that peeves privacy advocates, who argue the program will infringe upon rights and could lead to abuses or even false identification of people as criminals or terrorists.
"This involves mass scrutiny of the lives and activities of innocent people, a serious invasion of privacy and a violation of the core democratic principle that the government should not be permitted to violate a person's privacy, unless it has a reason to believe that he or she is involved in wrongdoing," said Carol Rose, executive director of the American Civil Liberties Union of Massachusetts.
Rose said that police should set limits on how the information will be used and conduct audits of its uses. "Technology by itself does not make us any safer," she added.
State Police said yesterday that whether to use the devices for background checks on individuals would be at the discretion of each trooper. Still, the police said, there will be little room for abuse of the system because all of the information contained in the database is culled from public records that police and even ordinary citizens could search on their own.
"It's nothing we don't have access to already," said Lieutenant Thomas Coffey.
"Instead of me having to go down to the registry of deeds in a particular county, I can now access this information via a BlackBerry," he added. "It's very critical because timely information is important to us, in order to provide a safer environment."
LocatePlus said the company will monitor every time the system is used and can lock individual BlackBerry devices out of its database if it suspects abuses.
State Police at Logan have been testing the BlackBerry devices with LocatePlus data since last year. Many troopers, including those at the airport, already carry hand-held computers that are tied into various law enforcement databases. Those databases allow an officer to check, for example, whether there are outstanding warrants for a person or he is on the US Justice Department's terrorism watch list.
But information that could tie individuals to crimes or to terrorists -- such as whether a former roommate is a suspected terrorist -- might be missing from law enforcement databases.
For example, if a trooper finds an abandoned cellphone, he could search immediately in LocatePlus's database for information on the individuals whose telephone numbers are stored in the phone. Gathering such information under normal circumstances would take several steps and more time.
Each of the 147 troopers assigned to Troop F will get a BlackBerry with LocatePlus access, said Phil Orlandella, a spokesman for the Massachusetts Port Authority, which owns and operates Logan.
Latorella said the State Police will pay $99 per unit per month for the computers and database access under a 12-month contract.
LocatePlus has 70 employees and pulled in $3.4 million in revenue last year, Latorella said. The company, founded in 1993, expects to make its first profit on projected sales of $6.5 million this year.
|
illusion of safety - or reality of fear?
HOMELAND INSECURITY
Baggage screening: Millions
spent on 'illusion of safety'?
Experts say politics, inability to admit
mistakes, behind wrong security fixes
Posted: July 23, 2002
1:00 a.m. Eastern
By Sherrie Gossett
© 2002 WorldNetDaily.com
Today, as the House Aviation Subcommittee examines the Transportation Security Administration's efforts to improve aviation security since 9-11 – and particularly its calls for more money – some experts are contending the issue is not sufficient funding, but rather, funding so badly misspent that air traveler safety hasn't appreciably improved since Sept. 11.
In an eventful week leading up to the hearing:
- John Magaw, who has headed up the newly created agency since Jan. 28, resigned, to be replaced by TSA Deputy Undersecretary and former Commandant of the U.S. Coast Guard James M. Loy.
- Rep. Dick Armey, R-Texas, has advocated exploring better technologies and has put forth a proposal to extend the Dec. 31 deadline by which date screening of 100 percent of passenger baggage must be in force at U.S. airports.
- Transportation Secretary Norman Mineta recently testified before Congress that the TSA has run out of money, and that air traveler security may be adversely affected if more money is not quickly appropriated.
But on the eve of the TSA hearings, world-renowned aviation security expert Isaac Yeffet – former director of global security for El Al Israel Airlines, Ltd. and a former director of the Israeli Secret Service – is sounding the alarm.
"Since 9-11, unfortunately nothing has been changed to increase the security of airliners," Yeffet told WorldNetDaily. "If there are not major changes, we will have to face another tragedy, God forbid."
"It's not smart to compromise by spending millions just so the TSA can say they're doing what the politicians and legislators wanted them to do," Yeffet said, "Do not state that there is a high level of security when we know it's not true. Let us tell the American people the truth."
At the center of the controversy is the contention that over $100 million has been spent on baggage-screening machines – as large as trucks, each costing some $1 million – that are not capable of detecting explosives. Some experts contend the high-priced machinery is soon destined for obsolescence, and serves only as a psychological deterrent for terrorists and a "save-face" for politicians.
"Don't use x-ray machines when you know it won't work," Yeffet warns.
Michael Boyd, CEO of the Boyd Group, an aviation research, consulting and forecasting company, was even more blunt: "The state of baggage-screening right now is chaos. It's a shambles, a complete shambles."
Boyd, who has testified before Congress several times, said, "It's congressional negligence. The DOT [Department of Transportation] has picked the wrong equipment to do the job and Congress has allowed them to make these decisions." Boyd also told WorldNetDaily that "Congress does not have the moral fortitude to say, 'We made a mistake,' the moral fortitude to go in a different direction, or to fire the people responsible."
Charles Slepian, CEO of the Forseeable Risk Analysis Center, said: "The technology they're using does not work, that much we do know." His company analyzes safety and security event data in an effort to identify how future incidents can be avoided.
"They're too slow, and they mistake tubs of jam for explosives. Credible evidence indicates they can't find explosives very well," he added.
Slepian was referring to the latest terminal evacuation due to CTX-machine related problems, on July 15 at Los Angeles International Airport. Officials ordered the partial evacuation of a terminal for about an hour. Harold Johnson, spokeman for LAX told WorldNetDaily the evacuation was caused by an InVision CTX scanning machine that mistook tubs of jam for explosives. It was the fourth such incident.
Baggage-screening is an important component of the Aviation and Transportation Security Act, signed by President Bush on Nov. 19, 2001. The legislation removed responsibility for aviation security from the FAA and established the Transportation Security Administration within the Department of Transportation, to handle all transportation security matters, including aviation security.
The law requires that TSA deploy enough explosive detection systems by the end of this year to screen all checked baggage. TSA first had planned to order 2,000 machines, but now has ordered about 1,100 bulk detection machines, such as the CTX or L3, and about 5,000 trace detection machines.
Some airports have complained that they will not be able to reconstruct their terminals by the end of the year to accommodate all the large bulk detection machines. Also problematic is the sheer weight of some machines, which will require floor reinforcement. Space is also a critical issue, with some airport managers claiming there will be practically no room left for passengers. Although the law provides flexibility in such cases, some airports are seeking an extension of the deadline.
According to the DOT Inspector General, of the 1,100 explosive detection machines that DOT says are needed by the end of the year, 1,025 have been ordered, 114 were supposed to be delivered by the end of June, 86 were delivered, and 29 have been installed. With the equipment installed under previous contracts, there are now 215 bomb detection machines operating at airports.
CT scans for baggage
The machines currently certified are made by InVision Technologies and L-3 Technologies. Both use technology derived from medical Computed Tomography (CT) to scan checked baggage. As the conveyor moves each bag through the machine, the system produces a scan projection X-ray image. From this image, the onboard computer determines which areas need "slice" images, taken by the rotating X-ray source. Using computer algorithms, the CTX system analyzes these 3-D slice images and compares their properties with those of known explosives. If a match is found, the system alarms and displays the object on the screen. An operator is then required to decipher the screen display.
The X-ray machines are able to produce precise 3-D images of dense objects, but cannot tell their chemical contents. This is true even of the most precise X-ray detectors, the ones that FAA certified as "Explosive Detection System" or EDS. In the jargon of the security professionals, X-rays, like the metal detectors, are only "anomaly detectors." They flag the suspicious objects as "possible explosives" which triggers an alarm and, in turn, the manual inspection of the luggage.
Common items such as magazines, chocolate and peanut butter can register as having the "density" of an explosive and thus trigger an alarm. This can cause costly evacuation. In addition, some experts contend that opening questionable luggage could be dangerous, as terrorists may have "booby-trapped" the bag to explode.
Although the machines are currently operating with a 17-30 percent false positive rate, a spokesman for InVision Technologies defended the technology as acceptable based on the fact that it was FAA certified.
But some have questioned the weight of FAA certification, saying that much of the criteria for certification was shaped around the CTX technology. Also, critics argue that since the certification was performed in 1994, and could only be accomplished by using two machines in tandem, such certification is not as impressive as it may sound. Further calls for elaboration and comment from InVision Technologies and the TSA were not returned.
"Here's the issue," said Boyd. "They're trying to make air transportation safer, with acceptable efficiency – but it isn't any safer, and they're killing efficiency." The analyst blames much of the problem on "strong political intervention."
"I have to say there are political agendas being pushed," he said. "Daschle is pushing for full disclosure of Bush's dealings 10 years ago, but he won't disclose what his wife made from lobbying for these companies."
Linda Daschle, wife of Senate majority leader Tom Daschle, D-SD, is a lobbyist for L-3 Technologies. In addition, Fred Roder, a former executive with InVision Technologies, is currently with the FAA, and has been accused by some of blocking the competition.
Says Yeffet, "If we can't have an X-ray machine we can rely on, how can we tell passengers with American air carriers that they are safe and secure?" He adds, "All it takes is one piece of baggage with explosives not seen and we'll be facing a tragedy with hundreds of people killed in an air explosion."
Boyd also contends that the FAA dragged feet looking into new technologies.
Yeffet is not just sounding an alarm, however, but believes he has found part of the solution to the problem. Yeffet has done research into what he contends is a revolutionary new technology that, if given a fair hearing, will transform aviation security in the United States. And Yeffet aims to take this information to government authorities.
The technology is the first stoichiometric detection and imaging technology. Stoichiometry refers to the deciphering of the chemical formulas of unknown substances. The technology can retrieve from 3 feet away, in a matter of seconds, the chemical formula and 3-D image of explosives through steel or soil; of cocaine through rice; or of anthrax through paper. The empirical chemical formulas of substances and their locations are obtained non-invasively, trans-barrier and online.
HiEnergy Technologies is the developer of the technology. Currently they are unaware of any other stoichiometric detector on the market or in the laboratory stages. Dr. Maglich, developer of the technology, explained that the physics involved in the process has been named Atometry.
He explained that the agents being sought are "first irradiated with fast neutrons tagged with alpha particles"
"The neutrons, in turn, cause the agents to emit prompt gamma rays back to the 'SuperSenzor,'" he added. The radiation involved is far less than that currently used in the CTX machines.
By electronically processing the alpha and gamma signals, formulas are obtained revealing the atomic proportions of carbon, nitrogen, and oxygen – key elements for deciphering explosives and organic compounds.
Ever since the early 1990s, experiments at four governmental laboratories – Naval Research Lab, Argonne National Lab, Los Alamos Scientific Lab and particularly the small Special Technologies Lab in Santa Barbara – have demonstrated the ability of online identification of both chemical elements and their imaging. This has been accomplished remotely (from 3 feet or more), through metal. The technique is called Associated Particle Imaging (API).
In 1999, a California research collaboration consisting of industrial and governmental laboratories reported further advance with API method at a White House Symposium on illicit substance detection. They were able to decipher – remotely and non-invasively, through ¾ inch of steel – not only the presence of all certain chemical elements in the concealed samples, but the accurate chemical formulas of explosives.
HiEnergy Technology's "SuperSenzor" is based on this atometery, which was developed in the period 1997-2002 at a cost of over $4 million, by the California Atometry Collaboration, a joint private sector-government-university research consortium led by HiEnergy. Private investors, tech industry and six governmental contracts (four Department of Defense, one Department of Energy, one U.S. Customs) have all contributed to the development of the project. HiEnergy has received no research and development funds from the TSA as yet.
HiEnergy Microdevices, whose product was originally linked to the detection of land mines (reviewed in Jane's International Defense Review in April 1998) subsequently held tests at the Santa Barbara laboratories of the Special Technologies Laboratory of the U.S. Department of Energy where anthrax simulant spores inside a sealed steel container were successfully identified.
The man responsible for these new developments, who also recently registered a patent for a revolutionary neutron microscope in 50 countries, is Dr. Bogdan Maglich, chief scientist and chairman of the board of HiEnergy Microdevices Inc. With a Ph.D. in high energy physics and nuclear engineering from MIT, Maglich worked closely with Nobel laureate Luis Alvarez and Vladimir Zworykin of RCA, known as the "Father of TV."
Maglich, the discoverer of the omega meson (the shortest-lived subatomic particle), has had work on particle physics, particle instrumentations as well as sub-atomic detection devices result in several major inventions. These include neutron photometry and the film-less spark chamber used in laboratories worldwide.
Closely associated on the current project are Dr Albert Beyerle, a physicist formerly with the Department of Energy as well as British-born radiation chemist Dr. George E. Miller, director of the nuclear reactor laboratory, University of California, Irvine. Both men have done pioneering work in related technologies.
Unlike the aforementioned, politically well-connected technologies, HiEnergy Technology has no inside political connections. The 1994 guidelines of the Gore Aviation Commission precluded even considering the technology. Then in 1998, the FAA Technical Center turned down the proposal to build a prototype of such a confirmation sensor. The reason given was that chemical identification of explosives to reduce the false alarm rates was "not in the FAA program priorities." The implication was that X-rays alone can detect explosives.
In response to what he believed were improprieties on the part of the FAA, Maglich filed a report in 2000 addressed to Rep. Christopher Cox, R.-Calif., chairman of the Select Committee on U.S. National Security. The report detailed alleged conflicts of interest and scientific misconduct by the FAA, including allegations of the compilation of grossly inaccurate "scientific" reports, the intentional misleading of Congress and the American people, and their subsequent impact on national security. The report included alleged violations of criminal law as well.
But in the wake of current and past criticism of the CTX machines, instead of looking at more advanced and cost-effective technologies, the TSA recently awarded a $1 million grant to Quantum Magnetics, an InVision Technology subsidiary, in the hopes that another technology produced by the same company may rectify the problems.
"By combining CT with QR sensors, we intend to reduce false alarm rates while improving overall performance on our FAA-certified systems," said Lowell J. Burnett, Ph.D., Quantum Magnetics' CEO and president.
The grant initiates the first six months of a potential 18-month research and development program that the company said has the potential to improve the performance of explosives detection systems However, the technologies advocated by Quantum Magnetics – including quadrupole resonance (QR), magnetic resonance (MR) and electromagnetic sensing technologies – are more limited than atometry.
- QR emits magnetic field signal and gets on the screen the magnetic response signal in a wave form. It builds into its memory the wave form typical of each explosive and recognizes it. The trouble is that its range is only two inches, thus it is considered out of the question for the checked luggage, but good for hand luggage only. However, a "standard" suitcase is 1 ft. x 2 ft. x 3 ft.
- Magnetic fields cannot penetrate even the thinnest sheath of metal, so QR is intrinsically incapable of "seeing" through anything foil-wrapped, let alone through metallic or metalized boxes. Also, the vicinity of metallic objects confuses the wave pattern, and 90 percent of suitcases contain solid metallic pieces. In addition, different explosive mix can give distorted waveform. Moreover, QR is intrinsically incapable of imaging – that is, it does not know the location of the objects. But this is somewhat compensated for by the fact that X-rays gives the precise position.
Despite the alleged "politics of funding" issues, Yeffet is determined to present the new technology to decision-makers in Washington, D.C. After investigating the technology and conducting his own tests, Yeffet signed on with HiEnergy as a consultant. But he contends his primary drive is for the safety of people.
"We're going to bring a revolution to aviation security. This is what I am going to do," he vowed.
Still, if security really hasn't improved at all, as Yeffet and others claim, why the messages of confidence in air safety from the TSA?
"It's time the public become aware of the fact [that] what they're watching now is show business," Slepian told WND. "What they're looking at in airports amounts to very little. The public has been misled. It has to be misled because otherwise it wouldn't travel, and the economy hinges on air travel. I don't endorse it, but that's the reason for it."
He adds, "Congress, and America, for another year, will have to cross their fingers, that al-Qaida doesn't strike again."
"CTX was certified in 1994. The public needs to be aware [that] for eight years we have known about the weaknesses. But government kept buying. Prior to 9-11, aviation and airlines were not using them because they knew the machines were incapable of satisfactory performance."
Meanwhile Boyd contends that Magaw's dismissal was the political version of a mob hit.
"It was quick, it was done to preserve the 'organization,' and he never saw it coming. When the coup de grace was administered, Magaw still had a full appointment book, and had no inkling that he was about to get whacked," said Boyd, who also contends the move was timed by Mineta to deflect criticism from himself. "This infantile tantrum came right after revelations about how the TSA had been squandering money like a drunken sailor near closing time."
Politics aside, Yeffet summarizes the unfolding controversy: "How can we accept risking the lives of innocent people? How can we allow it?"
|
hey Terrorists! don't look suspicious...No really?

A New Tack for Airport Screening: Behave Yourself
Exclusive: Airport screeners plan to shift tactics, focusing less on scissors and more on passenger behavior
By SALLY B. DONNELLY/WASHINGTON - Wednesday, May. 17, 2006 - TIME
In the four years since it was created, the Transportation Security Administration has been trying - and often failing - to find dangerous things that passengers might bring onto an aircraft. Now the TSA is aiming to become less obsessed with scissors and cigarette lighters and focusing more on passenger behavior. Government sources tell TIME that the agency will announce in the next few weeks that it will introduce a race-neutral profiling program at the country's busiest airports, among them New York's John F. Kennedy, Los Angeles International and Chicago's O'Hare. The program has an awkward title, Screening Passengers by Observation Techniques, but a clever acronym, SPOT. It has been tested over the last three years at several airports in the Northeast, including Boston's Logan Airport, where two of the 9/11 hijacking teams launched their operations.
Unlike the TSA's troubled and controversial use of computer databases to scan for individuals whose names occur on passenger "watch lists," SPOT is based on observing passenger behavior. George Naccara, the TSA's Federal Security Director who has been overseeing the SPOT program in Boston, is a big booster. "This system is conducted by trained personnel and closely monitored by supervisors," he says. "It provides another significant layer of security."
Here's how it works: Select TSA employees will be trained to identify suspicious individuals who raise red flags by exhibiting unusual or anxious behavior, which can be as simple as changes in mannerisms, excessive sweating on a cool day, or changes in the pitch of a person's voice. Racial or ethnic factors are not a criterion for singling out people, TSA officials say. Those who are identified as suspicious will be examined more thoroughly; for some, the agency will bring in local police to conduct face-to-face interviews and perhaps run the person's name against national criminal databases and determine whether any threat exists. If such inquiries turn up other issues countries with terrorist connections, police officers can pursue the questioning or alert Federal counterterrorism agents. And of course the full retinue of baggage x-rays, magnetometers and other checks for weapons will continue.
So far, the results for SPOT have been encouraging. According to Naccara, the SPOT program has resulted in the arrest of more than 50 people for having fake IDs, entering the country illegally or drug possession. It also has caught one of its own: several months ago a representative from the Department of Homeland Security tested the system by trying to get a fake weapon through the screening checkpoint; he was successfully stopped by a STOP screener. The TSA will also consider deploying SPOT teams to other transportation systems like train and bus stations.
The SPOT program comes none too soon, since the current TSA system of screening for threats on airplanes has been, well, spotty. Earlier this month TSA screeners not trained in the SPOT program pulled over three Marines in dress uniform for special screening. After being patted down and scrutinized closely, the Marines were finally let go and allowed to continue their duties - escorting the body of one of their colleagues killed in Iraq.
|
Magnetic resonance Imaging in Airports
|
quadrupole resonance & Terahertz imaging
The technology many say could revolutionize bomb detection is called quadrupole resonance, or QR. It is a variation of magnetic resonance imaging (MRI) technology, used to diagnose patients and scan baggage at airports, and can be used to detect explosives.
Source: SEA Homeland Security Capability Document Based on Data from HBCU Partners
The MRI machines found at hospitals are large magnets, which affect the magnetic properties of the nuclei of the water in the human body. Those magnetic properties enable the machine to generate an image.
QR, however, does not use a magnet. The technology operates under the principle that a magnetic resonance signal can be detected from explosives without applying a large external magnetic field.
This is how QR works:
A transmitter emits pulses of low-intensity radio waves.
Nuclei within the explosive are momentarily aligned with the radio waves.
After each pulse, the nuclei emit a characteristic radio signal, like an echo.
The signal is picked up, amplified and analyzed.
A computer issues a warning if it identifies a signal that is emitted only by explosives.
Bomb-Detection Technology Useful for Countermine Ops
Terahertz imaging comes into view
Field-Portable MRI Instruments:
Through the application of the new nanomaterial-based contrast reagents, the possibility exists for development of a small, lightweight, field-portable MRI imager. Such instruments would be useful in battlefield trauma diagnosis, rapid treatment and reduced mortality.
Defense and Homeland Security Applications at Luna Innovations
|
Fear is a force multiplier - Terror propagates the ever sprawling security industry
justifying the initiation Techno - Martial law, Global surveillance grid
Billions spent on Weapons detection, & they put Armed guards on planes!!!
It's OK though...The good guys [er CIA ? FBI?] ]have the guns...OH REALLY???
|
Most, if not all, domestic US flights are to have "air marshals" carrying firearms on board, President George W Bush confirmed on Thursday. This, and other airline security measures, follow the suicide hijackings on 11 September. President Bush made the announcement to airline workers in Chicago, but did not support the idea of arming pilots, as recommended on Wednesday by the US Airline Pilots Association. However, installing any weapons on aeroplanes is a gamble, say experts, and could actually increase the risk to passengers.
"The plans are perhaps going to cause an even bigger problem," says Edward Downs, a commercial aircraft pilot and editor of the industry publication, Jane's Avionics.
"Once you have introduced weapons, they could get into the wrong hands and then you have armed the terrorists. We go to a lot of effort to make sure weapons don't get onto planes," he says.
New Scientist
|
So let's get this straight, terrorists need weapons to hijack flights, right?
so...all they have to do is try to overpower the guys who are on the plane already
I mean what are the air marshall going to do?
SHOOT inside a pressurized plane!?
[see non lethal weapons, above, for a hint at the next stupidest option]
Analogic is a leading developer and manufacturer of complete, innovative systems for medical and security imaging. We supply Computed Tomography (CT) systems for a growing number of niche applications, including new large-bore systems for radiotherapy. We also invented the world's first 24-slice CT scanner for explosive detection, able to capture full three-dimensional images of all objects in a piece of checked luggage. We design and produce complete Digital Radiography (DR) systems for a customer, while our Anrad subsidiary develops and manufactures amorphous selenium-based flat-panel detectors for DR.Analogic
|
who are 'Analogic'?
it's the usual suspects
It's all connected
Border control - HAARP - Radar
Satellite Global positioning systems, Privatized intelligence companies
|
First - your luggage - now you are next - Total recall? Body Scanners
"such technology may be used in place of an intrusive search,
such as a body cavity search, when there is probable cause sufficient to support such a search"
American Civil liberties union
"Low radiation X-rays penetrate a quarter of a centimetre into the suspect's skin. It can reveal drugs, knives, guns and explosives under clothing.
In about six seconds the scanner produces a 360 degree image of the body without clothing.
Suspects' bodies show up as a light colour on a monitor while foreign objects are dark.
A raid in London this week lead to more than 30 arrests for cannabis possession, carrying a knife and handling of stolen goods. "
Dancers X-rayed at clubs
|
|
|
The estimated radiation dose to the lung or stomach from a single, full-body CT scan was similar to that received by some of the survivors of atomic bombs who had been exposed to the lowest levels of radiation during these disasters.
BBC
|
|
London airport uses revealing body scanner
Sunday 7th November, 2004
A body scanner in use at Heathrow Airport in London sees through passengers' clothing to spot hidden weapons or explosives, the Sunday Times reported.
The device produces a naked image of passengers by bouncing X-rays off their skin, which has raised privacy concerns among travelers and aviation officials. Its use had not been widely known, as new security measures at airports are not usually publicized.
The tall, filing cabinet-shaped device is used inside a curtained area where passengers are asked to assume several poses to register their image. Passengers are chosen on a random and voluntary basis, and those who refuse are subject to hand searches.
It was really horrible, said a female passenger who requested anonymity. It doesn't leave much to the imagination because you're virtually naked, but I guess it's less intrusive than being hand searched. A male traveler said he was shocked at what he saw and felt embarrassed.
Security officials say the scanner is far more effective than conventional metal detectors because it sees the outline of any solid object, even those made of plastic or ceramics.
The U.S. Transportation Security Administration has refused to deploy the x-ray machine until it can be modified to mask passengers' modesty. -
Big News Network.com
|
|
|
Backscatter X-Ray technology
The application of this new x-ray technology to airport screening uses high energy x-rays that are more likely to scatter than penetrate materials as compared to lower-energy x-rays used in medical applications. Althought this type of x-ray is said to be harmless it can move through other materials, such as clothing.
A passenger is scanned by rastering or moving a single high energy x-ray beam rapidly over their form. The signal strength of detected backscattered x-rays from a known position then allows a highly realistic image to be reconstructed. Since only Compton scattered x-rays4 are used, the registered image is mainly that of the surface of the object/person being imaged. In the case of airline passenger screening it is her nude form. The image resolution of the technology is high, so details of the human form of airline passengers present privacy challenges. - epic.org
|
|
Rapiscans Secure 1000 Body Scanning System is a safe, non-intrusive screening system that rapidly and accurately images metallic and non-metallic objects concealed on a persons body, enhancing security, while reducing the need for physical hands on searching.
The Secure 1000 allows the operator to detect threats by imaging explosive materials such as dynamite, C-4, Detasheet, as well as ceramics, graphite fibers, plastic containers, plastic weapons, glass vials, syringes, packaged narcotics, bundled paper currency, and even wooden objects. The individual being screened stands in front of the system for a 6 second front, rear and 2 side scans. The digital image is immediately displayed on the security operator's computer screen showing the shape and location of objects hidden under the clothing.
The Secure 1000 operates by scanning the subject with a narrow beam of x-rays. Some of these x-rays will be reflected by the body as backscatter in the opposite direction, and be gathered by sensitive x-ray detectors. Advanced image processing algorithms use this information to generate the images.
Too revealing or crucial for safety in planes?
'See through clothes' scanner gets outing at Heathrow
|
|
|
Lie detectors may be next step in airline security
Published on ZDNet News: November 17, 2005
A new walk-through airport lie detector made in Israel may prove to be the toughest challenge yet for potential hijackers or drug smugglers.
Tested in Russia, the two-stage GK-1 voice analyzer requires that passengers don headphones at a console and answer "yes" or "no" into a microphone to questions about whether they are planning something illicit. The software will almost always pick up uncontrollable tremors in the voice that give away liars or those with something to hide, say its designers at Israeli firm Nemesysco.
"In our trial, 500 passengers went through the test, and then each was subjected to full traditional searches," said Chief Executive Officer Amir Liberman. "The one person found to be planning something illegal was the one who failed our test."
The GK-1 is expected to cost between $10,000-$30,000 when marketed. A spokesman for Moscow's Domodyedevo airport, which is using a prototype, said "the tester (lie detector) has proved to be effective and we are in principle ready to use it."
The September 11, 2001 hijacking attacks have led to a slew of innovations designed to boost airline security. Liberman said several countries had expressed interest in the GK-1.
"Unlike conventional lie detectors such as the polygraph, this is minimally invasive, requiring hardly any physical contact," Liberman said, adding that the first stage of the test takes between 30-75 seconds.
Those that fail are taken aside for more intensive questioning and, if necessary, searches. Liberman said around 12 percent of passengers tend to show stress even when they have nothing to hide.
"Some may feel nervous because they have used drugs, while having no intention to smuggle drugs," he said. "The whole thing is performed in a low-key manner to avoid causing anxiety." - zdnet.com
|
|
Airline passengers face lie detector tests
By Adrian Blomfield in Moscow (Filed: 06/04/2006)
Millions of airline passengers travelling through Russia will soon have to take a lie detector test as part of new security measures. The technology, to be introduced at Moscow's Domodedovo airport as early as July, is intended to identify terrorists and drug smugglers. If successful, it could revolutionise check-ins.
At first, only passengers deemed suspicious will take the test Passengers will pick up the handset of a "truth verifier" machine while they are asked questions. Apparently the machine, developed by an Israeli company, can even establish whether answers come from the memory or the imagination.
The technology is being used by some insurance companies in Britain to screen telephone claims for fraud.
"We know that this could be uncomfortable for some passengers but it is a necessary step," said Vladimir Kornilov, the IT director for East Line, which operates the airport.
At first, only passengers deemed suspicious by the FSB, the security service that succeeded the KGB, will take the test. But it will eventually encompass all passengers.
"If a person fails, he is accompanied by a guard to a cubicle where he is asked questions in a more intense atmosphere," Mr Kornilov said.
The machine asks four questions. The first is for full identity, while the second, unnerving in its Soviet-style abruptness, demands: "Have you ever lied to the authorities?" It then asks if the passenger is carrying weapons or narcotics.
To cut delays to a minimum, passengers will take the test after putting their shoes and baggage through the X-ray machines and before retrieving them. Officials insist that it will take between 30 seconds and a minute. - telegraph.co.uk
|
|
|
Bush Turns to Big Military Contractors for Border Control
By ERIC LIPTON WASHINGTON, May 17 - NY Times
The quick fix may involve sending in the National Guard. But to really patch up the broken border, President Bush is preparing to turn to a familiar administration partner: the nation's giant military contractors.
Lockheed Martin, Raytheon and Northrop Grumman, three of the largest, are among the companies that said they would submit bids within two weeks for a multibillion-dollar federal contract to build what the administration calls a "virtual fence" along the nation's land borders.
Using some of the same high-priced, high-tech tools these companies have already put to work in Iraq and Afghanistan - like unmanned aerial vehicles, ground surveillance satellites and motion-detection video equipment - the military contractors are zeroing in on the rivers, deserts, mountains and settled areas that separate Mexico and Canada from the United States.
It is a humbling acknowledgment that despite more than a decade of initiatives with macho-sounding names, like Operation Hold the Line in El Paso or Operation Gate Keeper in San Diego, the federal government has repeatedly failed on its own to gain control of the land borders.
|
|
Through its Secure Border Initiative, the Bush administration intends to not simply buy an amalgam of high-tech equipment to help it patrol the borders - a tactic it has also already tried, at a cost of hundreds of millions of dollars, with extremely limited success. It is also asking the contractors to devise and build a whole new border strategy that ties together the personnel, technology and physical barriers.
"This is an unusual invitation," the deputy secretary of homeland security, Michael Jackson, told contractors this year at an industry briefing, just before the bidding period for this new contract started. "We're asking you to come back and tell us how to do our business."
The effort comes as the Senate voted Wednesday to add hundreds of miles of fencing along the border with Mexico. The measure would also prohibit illegal immigrants convicted of a felony or three misdemeanors from any chance at citizenship.
The high-tech plan being bid now has many skeptics, who say they have heard a similar refrain from the government before.
"We've been presented with expensive proposals for elaborate border technology that eventually have proven to be ineffective and wasteful," Representative Harold Rogers, Republican of Kentucky, said at a hearing on the Secure Border Initiative program last month. "How is the S.B.I. not just another three-letter acronym for failure?"
President Bush, among others, said he was convinced that the government could get it right this time.
"We are launching the most technologically advanced border security initiative in American history," Mr. Bush said in his speech from the Oval Office on Monday.
Under the initiative, the Department of Homeland Security and its Customs and Border Protection division will still be charged with patrolling the 6,000 miles of land borders.
The equipment these Border Patrol agents use, how and when they are dispatched to spots along the border, where the agents assemble the captured immigrants, how they process them and transport them - all these steps will now be scripted by the winning contractor, who could earn an estimated $2 billion over the next three to six years on the Secure Border job.
More Border Patrol agents are part of the answer. The Bush administration has committed to increasing the force from 11,500 to about 18,500 by the time the president leaves office in 2008. But simply spreading this army of agents out evenly along the border or extending fences in and around urban areas is not sufficient, officials said.
"Boots on the ground is not really enough," Homeland Security Secretary Michael Chertoff said Tuesday at a news conference that followed Mr. Bush's announcement to send as many as 6,000 National Guard troops to the border.
The tools of modern warfare must be brought to bear. That means devices like the Tethered Aerostat Radar, a helium-filled airship made for the Air Force by Lockheed Martin that is twice the size of the Goodyear Blimp. Attached to the ground by a cable, the airship can hover overhead and automatically monitor any movement night or day. (One downside: it cannot operate in high winds.)
Northrop Grumman is considering offering its Global Hawk, an unmanned aerial vehicle with a wingspan nearly as wide as a Boeing 737, that can snoop on movement along the border from heights of up to 65,000 feet, said Bruce Walker, a company executive.
Closer to earth, Northrop might deploy a fleet of much smaller, unmanned planes that could be launched from a truck, flying perhaps just above a group of already detected immigrants so it would be harder for them to scatter into the brush and disappear.
Raytheon has a package of sensor and video equipment used to protect troops in Iraq that monitors an area and uses software to identify suspicious objects automatically, analyzing and highlighting them even before anyone is sent to respond.
These same companies have delivered these technologies to the Pentagon, sometimes with uneven results.
Each of these giant contractors - Lockheed Martin alone employs 135,000 people and had $37.2 billion in sales last year, including an estimated $6 billion to the federal government - is teaming up with dozens of smaller companies that will provide everything from the automated cameras to backup energy supplies that will to keep this equipment running in the desert.
The companies have studied every mile of border, drafting detection and apprehension strategies that vary depending on the terrain. In a city, for example, an immigrant can disappear into a crowd in seconds, while agents might have hours to apprehend a group walking through the desert, as long as they can track their movement.
If the system works, Border Patrol agents will know before they encounter a group of intruders approximately how many people have crossed, how fast they are moving and even if they might be armed.
Without such information, said Kevin Stevens, a Border Patrol official, "we send more people than we need to deal with a situation that wasn't a significant threat," or, in a worst case, "we send fewer people than we need to deal with a significant threat, and we find ourselves outnumbered and outgunned."
The government's track record in the last decade in trying to buy cutting-edge technology to monitor the border - devices like video cameras, sensors and other tools that came at a cost of at least $425 million - is dismal.
Because of poor contract oversight, nearly half of video cameras ordered in the late 1990's did not work or were not installed. The ground sensors installed along the border frequently sounded alarms. But in 92 percent of the cases, they were sending out agents to respond to what turned out to be a passing wild animal, a train or other nuisances, according to a report late last year by the homeland security inspector general.
A more recent test with an unmanned aerial vehicle bought by the department got off to a similarly troubling start. The $6.8 million device, which has been used in the last year to patrol a 300-mile stretch of the Arizona border at night, crashed last month.
With Secure Border, at least five so-called system integrators - Lockheed, Raytheon and Northrop, as well as Boeing and Ericsson - are expected to submit bids.
The winner, which is due to be selected before October, will not be given a specific dollar commitment. Instead, each package of equipment and management solutions the contractor offers will be evaluated and bought individually.
"We're not just going to say, 'Oh, this looks like some neat stuff, let's buy it and then put it on the border,' "Mr. Chertoff said at a news conference on Tuesday.
Skepticism persists. A total of $101 million is already available for the program. But on Wednesday, when the House Appropriations Committee moved to approve the Homeland Security Department's proposed $32.1 billion budget for 2007, it proposed withholding $25 million of $115 million allocated next year for the Secure Border contracting effort until the administration better defined its plans.
"Unless the department can show us exactly what we're buying, we won't fund it," Representative Rogers said. "We will not fund programs with false expectations."
|
The next level: Brain manipulation
Using M.R.I.'s To See Politics On the Brain
New York Times
John Tierney
Apr 16, 2004
The political consultants discreetly observed from the next room as their subject watched the campaign commercials. But in this political experiment, unlike the usual ones, the subject did not respond by turning a dial or discussing his reactions with a focus group.
He lay inside an M.R.I. machine, watching commercials playing on the inside of his goggles as neuroscientists from the University of California, Los Angeles, measured the blood flow in his brain. Instead of asking the subject, John Graham, a Democratic voter, what he thought of the use of Sept. 11 images in a Bush campaign commercial, the researchers noted which parts of Mr. Graham's brain were active as he watched. The active parts, they also noted, were different from the parts that had lighted up in earlier tests with Republican brains.
The researchers do not claim to have figured out either party's brain yet, since they have not finished this experiment. But they have already noticed intriguing patterns in how Democrats and Republicans look at candidates. They have tested 11 subjects and say they need to test twice that many to confirm the trend.
"These new tools could help us someday be less reliant on cliches and unproven adages," said Tom Freedman, a strategist in the 1996 Clinton campaign, later a White House aide and now a sponsor of the research. "They'll help put a bit more science in political science."
In the experiment with Mr. Graham, researchers exposed him to photographs of the presidential candidates, commercials for President Bush and John Kerry, and other video images, including the "Daisy" commercial from 1964. In that advertisement, promoting Lyndon B. Johnson against Barry Goldwater, images of a girl picking petals from a daisy were replaced by images of a nuclear explosion.
When Mr. Graham emerged from his hourlong session in the magnetic resonance imaging machine, the researchers had no questions for him, but he did field an old-fashioned one from a reporter wondering what had most impressed him. He cited two images: the Sept. 11 segment of the Bush commercial and the nuclear explosion that the "Daisy" advertisement suggested would be a consequence of electing Mr. Goldwater.
"I was shocked at how much political capital Bush is trying to make out of 9/11," Mr. Graham said. "But I found it kind of interesting that Johnson was using the same kind of technique against a Republican."
The researchers had already zeroed in on those images and their effect among Democrats on the part of the brain that responds to threats and danger, the amygdala. Mr. Graham, like other Democrats tested so far, reacted to the Sept. 11 images with noticeably more activity in the amygdala than did the Republicans, said the lead researcher, Marco Iacoboni, an associate professor at the U.C.L.A. Neuropsychiatric Institute who directs a laboratory at the Ahmanson Lovelace Brain Mapping Center there.
"The first interpretation that occurred to me," Professor Iacoboni said, "is that the Democrats see the 9/11 issue as a good way for Bush to get re-elected, and they experience that as a threat."
But then the researchers noted that same spike in amygdala activity when the Democrats watched the nuclear explosion in the "Daisy" spot, which promoted a Democrat.
Mr. Freedman suggested another interpretation based on his political experience: the theory that Democrats are generally more alarmed by any use of force than Republicans are. For now, Professor Iacoboni leans toward this second interpretation, though he is withholding judgment until the experiment is over.
Mr. Freedman and William Knapp, a strategist with both Clinton presidential campaigns and the Gore campaign in 2000, turned to this technology after consulting with Mr. Freedman's brother, Dr. Joshua Freedman, an assistant professor of psychiatry at U.C.L.A., who was less than impressed by the methodology of political consultants.
"It seemed so last century," Professor Freedman said. "Consultants were quoting Freud as if it was cutting edge. It was all about interpretation instead of using new technology to measure what's actually happening in the mind."
Professor Freedman and the two political consultants formed a company, FKF Research, and provided a grant for an experiment led by Professor Iacoboni, a neuroscientist known for his work mapping parts of the brain activated when people empathize with others. He, Professor Freedman and a U.C.L.A. colleague, Jonas Kaplan, plan to publish the results in a scientific journal.
"In the past decade we've built up all this knowledge of how the brain works," Professor Iacoboni said, "and now it's exciting that we can finally start applying it to social issues."
One of the most striking results so far is the way subjects react to candidates after seeing a campaign commercial. At the start of the session, when they look at photographs of Mr. Bush, Mr. Kerry and Ralph Nader, subjects from both parties tend to show emotional reactions to all the candidates, indicated in the ventromedial prefrontal cortex, an area of the brain associated with reflexive reactions.
But then, after the Bush campaign commercial is shown, the subjects respond in a partisan fashion when the photographs are shown again. They still respond emotionally to the candidate of their party, but when they see the other party's candidate, there is more activity in the rational part of the brain, the dorsolateral prefrontal cortex. "It seems as if they're really identifying with their own candidate, whereas when they see the opponent, they're using their rational apparatus to argue against him," Professor Iacoboni said.
The neuroscientists warned against drawing conclusions until the experiment was over. They said the results would mainly point the way for future research, and other neuroscientists echoed their caution.
"Brain imaging offers a fantastic opportunity to study how people respond to political information," said Jonathan D. Cohen, director of the Center for the Study of Brain, Mind and Behavior at Princeton. "But the results of such studies are often complex, and it is important to resist the temptation to read into them what we may wish to believe, before our conclusions have been adequately tested."
Shanto Iyengar, director of the Political Communication Lab at Stanford, said there were so many kinds of images and other stimuli in a political commercial that it was notoriously difficult for any kind of research to pinpoint effects. But Professor Iyengar said the M.R.I. technology offered a promising tool.
"Academic research in political science into the effects of campaign advertising is 90 percent bogus, relying as it does on self-reported exposure to a multitude of disparate messages and images," he said. "Any efforts to isolate viewers' actual responses to ads -- be they neurological, verbal or behavioral -- is a step in the right direction."
Though new to political advertising, brain imaging has been used to analyze other kinds of reactions to commercials, both by "neuromarketers" selling services to corporations and by academic researchers like Read Montague, who has studied brain responses to soft-drink advertising. He said research like Professor Iacoboni's could help expose manipulative techniques during political campaigns.
"This research can show how a candidate is unfairly targeting the weaknesses and foibles of voters, and that can be empowering," said Professor Montague, director of the Human Neuroimaging Laboratory at the Baylor College of Medicine.
Of course, political consultants could also use this technology to create more manipulative commercials, though Mr. Freedman and Mr. Knapp say they do not hope for partisan advantage from their research.
"We just want to start exploring this new frontier," Mr. Knapp said. "We know we can't rely just on what people say in polls and focus groups. They tell us over and over that they hate negative advertising, but we know they respond to it. It would be nice to figure out what's actually going on inside their heads."
|
|
Brain Fingerprinting - The fight against crime gets real sinister...
|
|
Brain Fingerprinting testing detects information stored in the human brain. A specific, electrical brain wave response, known as a P300, is emitted by the brain within a fraction of a second when an individual recognizes and processes an incoming stimulus that is significant or noteworthy. When an irrelevant stimulus is seen, it is seen as being insignificant and not noteworthy and a P300 is not emitted. The P300 electrical brain wave response is widely known and accepted in the scientific community. There have been hundreds of studies conducted and articles published on it over the past thirty years. In his research on the P300 response, Dr. Farwell discovered that the P300 was one aspect of a larger brain-wave response that he named a MERMER (memory and encoding related multifaceted electroencephalographic response). The MERMER comprises a P300 response, occurring 300 to 800 ms after the stimulus, and additional patterns occurring more than 800 ms after the stimulus, providing even more accurate results.
Brainwave science
|
Two new studies, both using event-related potentials (ERPs), report that criminal psychopaths and teenagers with conduct disorder have abnormal responses to stimuli.
Kent Kiehl and colleagues studied a particular brainwave response, known as the P300, in 11 psychopathic and 10 non-psychopathic prison inmates. (Psychopaths, who are characterized by egocentricity, shallowness, manipulativeness, deceitfulness, selfishne ess, and lack of empathy, remorse, or guilt, are generally more dangerous and far less responsive to rehabilitation efforts than other prisoners.)
The researchers measured subjects response to a visual oddball task, in which the participants responded to a low-probability visual stimulus. The P300 response to an oddball task, Kiehl et al. say, is thought to be sensitive to changes in the alloc cation of attentional resources and processes involved in contextual updating and decision making.
The researchers report that among non-psychopathic subjects, the amplitude of the P300 was larger when target stimuli appeared than when other stimuli appeared. In contrast, they say, psychopaths failed to show reliable P300 amplitude differences betwe een the target and non-target conditions, and exhibited a smaller amplitude P300 in response to target stimuli than did other subjects. In addition, the psychopaths P300 response was less lateralized, which the researchers say is interesting in light of f f evidence indicating that psychopathy is associated with weak or abnormal lateralization of the cerebral hemispheres.
The researchers also found that the psychopaths exhibited an abnormal late centro-frontal negative wave (N550) when target stimuli were presented. This is the first study to identify this abnormality among psychopaths doing a task that did not require lin nguistic processing.
Crimetimes
|
BFP is a scientific methodology for establishing knowledge or non-knowledge of a particular event. It has been utilized in the American criminal system to establish guilt, and also as an advanced Neuromarketing method. It has been publicly advocated by scientists and lawmakers as an efficient solution for air travel security. - Acclairism
|
|
|
|
"
The P300 response can be manipulated . Current non-lethal
investments over state their potential. Large contractors blur the focus in order to maintain
research allocations..."
|
|
OVERLOOKED MIND CONTROL RESEARCH
by : Thomas V. Sobczak, Ph.D., PE, FSME, FIAE [backed up]
INTRODUCTION
Sobczak is researching and experimenting with code string logic and RF transmission
methods to create non-lethal weapons that affect people. We reason, after an Internet
search, that sensors in weapons systems are security risks. The following explains a small
portion of my research and discusses the potential to affect people using code strings
transmitted by radio frequencies and non-ionizing radiation. The Israelis, Russians and
Germans are experimenting in this area. Pseudo-soliton waves and other electronic
stimuli can be produced from soft code strings that stimulate on board equipments to
condition responses of users. Sobczak created a prescribed wave that causes ocular
dysfunction. Focused oscillations cause an individual concentrating upon a video display
screen to develop a severe headache when my code takes control of the snap back
mechanism (screen refresh) of a Video Display Unit. Similarly, oscillating electric powered
devices causes neglect and disorientation by those within range. Strange things occur
when non-ionizing radiation leaking from power lines is harnessed to pulse signal.
BACKGROUND
X rays and gamma rays are found at the high end of the frequency spectrum. The electric
potential os the human brain, the most important of nature's phenomena, is located at the
low end of the frequency spectrum. Sobczak has affected brain functions by developing
software produced low frequency waves. Our goal was to alter psychological states
(produce mood changes) and to transmit stimuli that trigger suggestions and/or commands
directly into the human brain. The ability to accomplish the foregoing dwarfs both the
atomic bomb and SDI. Such technology can be used to achieve political and military goals
without force of arms.
In 1962 there was much excitement about the Soviet microwave attack upon the American
Embassy in Moscow. The attack was a test that harassed diplomats and caused worry
about the latent effect microwaves would produce. The ploy was a success. The question
was raised whether the USSR had conceived a technique using microwave frequencies for
psychological purposes. Were the Americans pressed into service as guinea pigs?
Discussion centered about the ability of microwaves to penetrate the blood-brain barrier.
Thermal effects are so small that the human brain does not appear be affected. As a
historical note, the record shows that embassy employees were indemnified for damages,
real or imagined, to their health. American Defense responded by beginning Project
Pandora.
The Defense universe and the CIA became paranoid about loss of mind manipulation
leadership. MKULTRA (ARTICHOKE), MKDELTA, MKNAOMI, MKRESEARCH,
BLUEBIRD (renamed ARTICHOKE by DCI) and a continuation of the earlier CHATTER
Project (1947) were started over time. The sponsored activities might be compared to an
attempt to seduce a woman. They assumed that plain women (Complex Systems) would
more readily respond than beautiful women. What these experts missed was the fact that
everyone ignored the beautiful woman because her beauty is considered unapproachable.
In fact the beautiful woman was lonely and eager to be seduced. Hundreds of millions
were/are wasted complicating mind control solutions. Project objectivity was affected by
researcher and sponsor perceptions.
It was later documented that electromagnetic fields raising body temperature by less than
.1 degree Celsius cause somatic change. A minimal increase in body temperature had an
effect on human functioning. More astonishing was the fact that e;ectromagnetic effects
were deemed significant. In 1963 Robert Strausz-Hupe accepted the premise of A.S.
Davydov concerning EXCITONS. His book, PROTRACTED CONFLICT, an suggested a
new era of psyops philosophy that had not been previously considered. It was ignored by
the experts at the time.
Chemical, physiological and behavioral changes occur within "windows" of frequency and
energy continua (A.S. Davydov in QUANTUM THEORY, 1967.) This concept was
described in his 1962 work THEORY OF MOLECULAR EXCITONS. His concept Quantum
Theory is upgraded in his 1971 volume of the same title. In 1982 he published his
BIOLOGY AND QUANTUM MECHANICS. One of the windows discussed is connected to
biological rhythms of humans. Another is at the level of the human electroencephalogram,
i.e., in the range of extremely low radio and sound waves (+/- 20 hertz).
These early findings were thought to require energy amplification in the order of magnitude
of twelve. This level of amplification was not feasible in light of the than current
understanding of the technology involved. No one took credit for the discovery which
proved this false postulate. The postulate was accepted without further research.
The original amplification model was based upon the premise that electromagnetic waves
interact with tissue in a linear fashion. The term soliton appeared. Research proved the
molecular vibrations caused by stimulating extracellular electromagnetic field properties are
non-linear. The vibrations take the form of soliton waves transferring energy along long
molecular chains. In 1971 William Kintner hinted at a Soviet breakthrough . The soviets
acknowledged this in 1983 when P.G. Drazin published SOLITONS
In 1982 that term soliton achieved technical acceptance in the McGraw Hill
scientific-technical dictionary: "A soliton wave .... propagates without dispersing its energy
over larger and larger regions of space." Restated, a soliton wave propagates suddenly
acquired energy, or energy imparted by a shock, without dispersing it. My research found
that soliton waves began being considered relevant by the military in high energy physics
and in the fusion program in 1985.
In biology solitons occur as electro-solitons and as acoustic solitons. They form only at
certain high- and low-energy levels, or windows. Solitons are dynamically stable "spikes".
They participate in vital processes. Solitons have long lifetimes. Their vibration has a long
persistence. These characteristics contribute to the formation of a soliton by a boost of
energy without a twelve order of magnitude increase suggested in the linear assumption.
The soliton allows extracellular disturbances such as acoustic or electromagnetic bursts to
be propagated across the cell membrane. Nonlinearities in molecular dynamics rather then
chemical kinetics unlock the puzzle. As a form of corruption or as a anti-corruption tool one
must visualize the human brain and its environment as structures of electronic waves.
Assume shock waves create solitons. Next imagine that modern electronics can be
designed and/or programmed to create a range of resonances utilizing the flexibility, speed
and accuracy inherent in the circuitry of a computing device and certain electronic
components.
Sobczak defined frequencies appropriate to repel aggression as well as available options
for transmission both to the target and then across the blood-brain barrier to brain cells.
Brain cells will be reachable diversely, flexibly and routinely. Mind manipulation as a
non-lethal weapon works. The P300 response can be manipulated. Current non-lethal
investments over state their potential. Large contractors blur the focus in order to maintain
research allocations.
Research about the relationship of microprocessor and board devices to cross-membrane
phenomenon is not documented anywhere in unclassified publications. Research involves
a high risk but results in enormous payback to secure fielded weapon systems from
aggression that subverts the abilities of the operator. One might suggest that a new
phenomenon has been discovered. Sobczak has created a soft code weapons capable
of being aimed and triggered to produce effects on people. We have yet to determine the
long term affects of the results produced.
Russian mathematicians have been concerned with solitons (initially referred to as
EXCITONS) long before Americans became interested. If a literature search is an
acceptable means of determining interest, American scientists are still disinterested. It is
conceivable that Davydov, Drazin and Boris Ponomarev functioning under the wing of Uri
Andropov achieved workable results which warranted testing long before publication. The
soliton topic remains a focal point of research by Drazin as indicated by his 1988
SOLITONS: INTRODUCTION AND APPLICATION from the winter school conference in
South India. Could this be the motive behind the original attack of microwave transmissions
that involved the U. S. Embassy in 1962?
Writings about soliton research in the United States is limited. Albert F. Lawrence and W
Ross Adey appear in the technical journal NEUROLOGICAL RESEARCH in 1982. Dr Adey
was chief of research at the US Veterans Hospital in Loma Linda, CA. The technical article
reports the effects of testing a Russian mind control device (LIDA Machine) on American
Veterans. A 1977 book by George Behefi titled ELECTROMAGNETIC VIBRATIONS,
WAVES AND RADIATION might be a reference text. Behefi led Sobczak to a book
authored by a Russian. V. S. Vavilov explained RADIATION EFFECTS IN
SEMICONDUCTORS AND SEMICONDUCTING DEVICES. Sobczak did not have
resources to continue this line of research. An earlier work by David Nachmansohn (1975)
titled CHEMICAL AND MOLECULAR BASIS FOR NERVE ACTIVITY turned Sobczak to
the efforts of Eberhard Neumann and Guenther Gerisch at the Max Planck Institute for
Biochemistry (Martinsried bei Muenchen).
These German researchers also discovered that cell membranes can be crossed. They
discovered that a shock wave passing through an electric field can create ultra quick
processes within the cell membrane. These "jumps in the field" allow genes to be
transmitted and cells to be fused. (feldspruenge = spike = soliton??).
The differential in the tension of the inner and outer membrane is said to average 1/70,000
volt. This corresponds to 70,000 volt per membrane thickness of one centimeter. In his
1983 work Drazin indicated the true thickness of a membrane is .1 to the -8 centimeter.
Drazin's discovery appears to be accidental but contributes to the research which followed.
Documented research requires measurements of events not lasting more than one
nanosecond. Various authors have suggested that solitons increase permeability of
membranes to a degree. The Germans proved it possible to genetic engineer
approximately fifty cells into one cell with fifty nuclei and a single membrane.
Russian, American, and German scientists successfully entered a membrane
independently. It appears that in a universe of narrowing technology we could state that
when the time comes for a fundamental innovation, discovery or invention to occur, it will
occur in several different places at different times involving independent researchers who
do not know of the other's efforts due to political or military security considerations.
Sobczak using the experience of others created COTS devices that affect computers,
telecommunications and people.
DIDDLING WITH THE BRAIN
A future explanation of Sobczak's COTS successes.
1. Capture and modification of the refresh rate (snap back mechanism) of a video tube.
2. Disorientation of people using:
a. Light
b. Sound
3. Stimulating vibrations in a metal filling in a tooth:
a. Pain
b. The voice of God
4. Creating nerve synapse response
|
|
|
"You're guilty - The machine say's so!"
What this means is:
Using RF via the monitor, a small electronic pulse generator or voice to skull technology - your brain can be made to respond with a given P300 brainwave at any appropriate moment, using these methods anyone can be framed for a crime they didn't commit...
or as an indicator of mental illness, which could prove very politically useful in locking away dissidents.
|
|
|
Mind Manipulation Research -
The Human Mind is subject to attacks using RF, microwave and non-ionizing radiation. ACC has experimented with anbd produced the means to condition the actions of computer users. ACC research has affected people by transmitting pulsed RF and microwave at them.
mindjustice.org
"It is possible to manipulate the nervous system of a subject by
pulsing images displayed on a nearby computer monitor or TV set. For the
latter, the image pulsing may be imbedded in the program material, or it
may be overlaid by modulating a video stream, either as an RF signal or as
a video signal. The image displayed on a computer monitor may be pulsed
effectively by a simple computer program. For certain monitors, pulsed
electromagnetic fields capable of exciting sensory resonances in nearby
subjects may be generated even as the displayed images are pulsed with
subliminal intensity."
read US patent
|
The voice of God? or just a sales pitch?
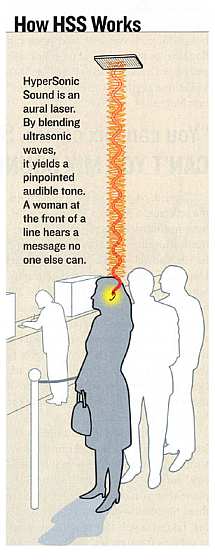
|
sound to skull technology
A new ultrasound system can zap a laserlike channel of sound over hundreds of feet to just one pair of ears in a crowd--a perfect pitch for marketers.
Elwood (Woody) Norris hangs out of a third-floor window of an office building in New York. In his hands is his latest invention, the HyperSonic Sound emitter. Seventy feet away, on the opposite side of Fifth Avenue, two FORBES staffers are told to stand and listen. At first we hear only the usual sounds of traffic, then, suddenly, the taxi honks are joined by bird shrieks and gurgling streams of a rain forest. The jungle sounds are so loud that, were they from a conventional loudspeaker, hundreds of pedestrians would be able to hear them.
Remarkably, only we two can.
After a couple of steps to the right, the jungle fades out. Then Norris pans his emitter back to us, and our heads fill with the crisp pop of a soda can being opened and poured into a glass of ice. "Isn't that cool?" Norris shouts. (It's his trademark phrase: "Idn'tatcool?") He grins, revealing unnaturally white teeth. "Imagine that coming out of Coke machines."
Now Hear This
We hold these freedoms to be self-evident...
Patent For Microwave
Voice-To-Skull Technology
American Technologies Corporation
|
Is the P300 Brainwave response what certain people
are naming 'the buy button in the brain'?
the brainWave manipulation is also evident during the process known as
Neuromarketing
pressing the 'buy button' in the brain
Neuromarketing is a controversial new field of marketing which uses functional Magnetic Resonance Imaging (fMRI) a medical technology -- not to heal, but to sell products. A BrightHouse Institute for Thought Sciences news release issued June 22, 2002 explains that it uses fMRI to identify patterns of brain activity that reveal how a consumer is actually evaluating a product, object or advertisement. Thought Sciences marketing analysts use this information to more accurately measure consumer preference, and then apply this knowledge to help marketers better create products and services and to design more effective marketing campaigns.
neuro-marketing [ $ ]
|
|
|
When Peter Graser underwent an MRI scan at Emory University, doctors weren't looking for disease.
Instead, brain researchers flashed images --- Madonna, broccoli, sushi, a Ford truck, a golden retriever, Bill Clinton, Coca-Cola --- before the 37-year-old Marietta resident's eyes as he lay inside the coffin-like tube of the magnetic resonance imaging machine.
The scientists discovered a biological clue to what drives consumers: Whenever Graser and a dozen other study volunteers saw a picture they particularly liked, their brains showed increased activity in the medial prefrontal cortex --- an area associated with preference, or sense of self.
On this Super Bowl Sunday, when advertising swells to a fever pitch, the researchers' conclusion is especially appropos: What really makes us loyal purchasers is a brand that reflects our self-image, not a product's taste, size, color or convenience.
|
|
The study, funded through the Atlanta consulting firm BrightHouse by an undisclosed Fortune 500 client, has stirred up controversy about the emerging --- and some say Orwellian --- field of "neuromarketing." Scientific tools such as MRI scanners, which allow researchers to peer into the brain and better understand depression, addiction, autism and schizophrenia, should not be used by Coca-Cola, McDonald's or Ford to entice people to buy more of their soda, french fries or sport utility vehicles, critics say.
"It's wrong to use medical technology for marketing and not for healing," said Gary Ruskin, executive director of Commercial Alert, a Portland, Ore.-based nonprofit organization that has worked to bar advertising from schools and other public areas. "We have epidemics of obesity, diabetes, alcoholism, gambling and smoking --- all tied to marketing. Any increase in the effectiveness of advertising can be devastating to the public."
Advertisers Probe Brains, Raise Fears
Neuromarketers Search For
'Buy Button' In The Brain
more from Commercial alert [thanks to Rense.com]
Is it your Brain?
Strange Orwellian Telescreens Debut At UK Supermarkets
|
Will people walking through Shopping malls & driving along freeways be bathed in FMRI, constantly urging us to feel a certain way? constantly scanning us for 'abnormalities' & labelling as 'terrorists'?

Brainwave the ultimate security key
By Michale Comte - December 15, 2005
RESEARCHERS hope to soon be able to use brainwaves to unlock doors and access bank accounts. Some companies are already offering iris recognition systems that many countries want to put into biometric passports. But Ottawa-based Carleton University researcher Julie Thorpe wants to take the idea further. She says it is possible to do away with key cards, numbers and a litany of other security tools that allow people to retrieve bank money, access computer data or enter restricted buildings.
"A user would simply think their password," said Ms Thorpe, who hopes to develop the first biometric security device to read your mind to authenticate users.
Her idea, yet to be proven viable for commercial use, assumes that brainwave signals, like fingerprints, vary between people, even when they think alike.
"Everyone's brainwave signal is a bit different even when they think about the same thing. They're unique just like fingerprints," she said.
While people may be tricked into giving up passwords, smartcards may be lost or stolen, as can biometric templates stored on computers, so-called "passthoughts" are unique.
A user would only have to think up a different password and save it on a computer, Ms Thorpe said, describing what would become the world's first changeable biometric security tool. The doctoral student is working with leading Canadian security technology researcher Paul Van Oorschot in Ottawa to turn her idea into reality. Her research builds on basic brain-computer interfaces to help paralysed patients communicate.
Whereas slight differences in brainwave patterns created difficulties for researchers trying to build universal tools that could translate thoughts into computer commands, these peculiarities make brainwaves ideal for security applications.
"You could use a sound or music or childhood memory as your pass. You could even flash someone an image to help them remember their passthought," Ms Thorpe said. Ms Thorpe must still prove that people can reproduce clear, concise signals repeatedly. "Often, unconscious thoughts, maybe a song in the back of your mind, may blur a signal," she said.
Also, current brain-computer interfaces are not yet up to the task. The latest electroencephalogram (EEG) hardware, which measures electrical signals in the brain, consists of a costly bowl-shaped cap dotted with electrodes. "It's not very fashionable, looks like a polka-dot swimming cap," Ms Thorpe said, noting how refinements are in the works. - news.com.au
|
|
300/MERMER (Memory and Encoding Related Multifaceted Electroencepholagraphic
Response),
Stimulating the inner ear can change P300 brainwave pattern
Eric Courchesne of the University of California at San Diego has found significant impairments in auditory processing in autistic individuals using P300 brain wave technology. The P300 brain wave occurs 300 milli-seconds after the presentation of a stimulus.
(The 'P' refers to the positive polarity of the brain wave.) The P300 is associated with cognitive processing, and this brain wave is considered an indication of long-term memory retrieval. Edelson et al. (1999) examined auditory P300 activity prior to and three months following auditory integration training (AIT).
Three autistic individuals participated in the experimental AIT group and two autistic individuals participated in a placebo group. Prior to AIT, all five individuals had abnormal auditory P300 activity, indicating an auditory processing problem. Three months following AIT, the results showed dramatic improvement in P300 activity for those who received AIT (i.e., a normalization of P300 activity) and found no change in those who received the placebo.
Auditory Processing Problems in Autism
Sudarshan Kriya and related practices (SK&p) in the Treatment of Depression
PMS, EEG, AND PHOTIC STIMULATION
|
|
|
|
Remote-Controlled Humans
LOS ANGELES - Smiling nervously, the young woman walks forward in a straight line. Suddenly, she veers to the right. She stumbles and stops, attempting to regain her balance, and continues to walk forward. And then she veers off to the left.
No, she's not intoxicated. The young lady's vestibular system, which controls her sense of movement and balance, has been thrown off-kilter by two weak electrical currents delivered just behind her ears.
This sort of electrical stimulation is known as galvanic vestibular stimulation, or GVS. When a weak DC current is delivered to the mastoid behind your ear, your body responds by shifting your balance toward the anode. The stronger the current, the more powerful its pull. If it is strong enough, it not only throws you off balance but alters the course of your movement. - Forbes
|
|
|